...
KRL is the language in which rulesets are programmed. Picos run KRL using the event evaulation cycle. Rules in KRL are "event-condition-action" rules because they tie together an event expression, a condition, and an action. Event expressions are how rules subscribe to specific events on the pico's event bus. KRL supports complex, declarative event expressions. KRL also supports persistent variables, which is how developers access the pico's state. KRL developers do not need a database to store attributes for the pico because of persistent variables.
KRE
...
Pico Engine
The pico engine is a host or container engine for picos. A given instance of KRE the pico engine can host any number of picos. KRE is the The pico engine that makes picos work. KRE Pico Engine is an open source project, hosted on Github.
KRL rulesets are usually hosted online. Developers register the URL with KRE a pico engine to create a ruleset ID or RID. The RID is what is installed in the picoA given ruleset can be installed in any number of picos. When the pico runs, it the engine gets the ruleset source, parses it, optimizes it, and executes it.
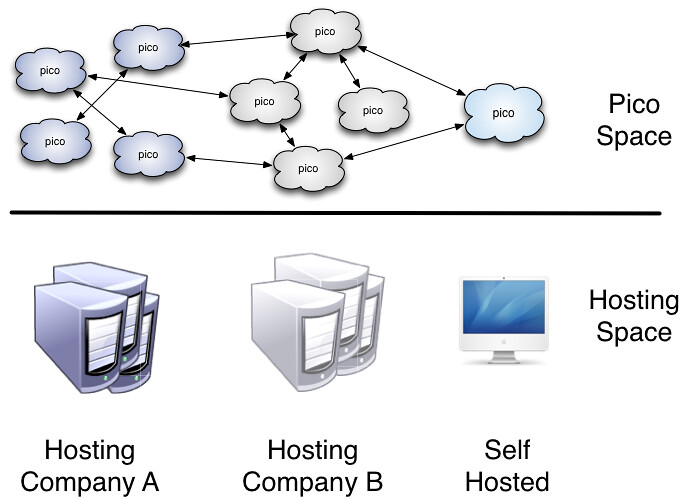
The diagram below shows an important property of pico hosting. Picos can have communication relationships with each other even though they are hosted on different instances of KRE. The KRE the pico engine. Pico engine instances need have no specific relationship with each other for the picos they host to interact.
This hosted model is important because it provides a key component of ensuring that picos can run everywhere, not only in one organization's infrastructure.
Conclusion
Picos present a powerful model for how a decentralized, heterarchical, interoperable Internet of Things can be built. Picos are built on open-source software and support a unbiased hosting model for deployment. They have been used to build and deploy several production systems, including the Fuse connected-car system. They provide the means for giving people direct, unintermediated control of their personal data and the devices that are generating it.
...